Data communication is making new progress on a new horizon. The HTTPS proxy is a dynamic transition mode, which aims to reduce the gap between communication fluency and data security online. For more secure data transmission, lots of researches have found that proxies play a crucial role.
In this article, we’ll delve into the full understanding of HTTPS proxy. How does an HTTPS web proxy work and why do you need it, besides, understand its role in ensuring a secure online experience.
Understanding HTTPS
HTTPS, or Hypertext Transfer Protocol Secure, is an internet communication protocol that protects the confidentiality and integrity of data between the user’s computer and the site. Websites that are HTTPS-secured apply encryption to protect the exchange of data, ensuring that the data is not tampered with or eavesdropped on.
What Is An HTTPS/SSL Proxy?
An HTTPS proxy, also known as an SSL proxy, is a type of proxy server that is capable of handling HTTPS requests from users and establishing a secure connection to the requested websites. People usually divide proxy types according to two basic standards: connection method or device types that act as proxy. The SSL presents a Secure Sockets Layer. It is the “S” in HTTPS, which means the HTTPS is an SSL-based hypertext transfer protocol. SSL or HTTPS proxy indicates that you use an HTTPS protocol to connect through the proxy server.
How Does An HTTPS Proxy Work?
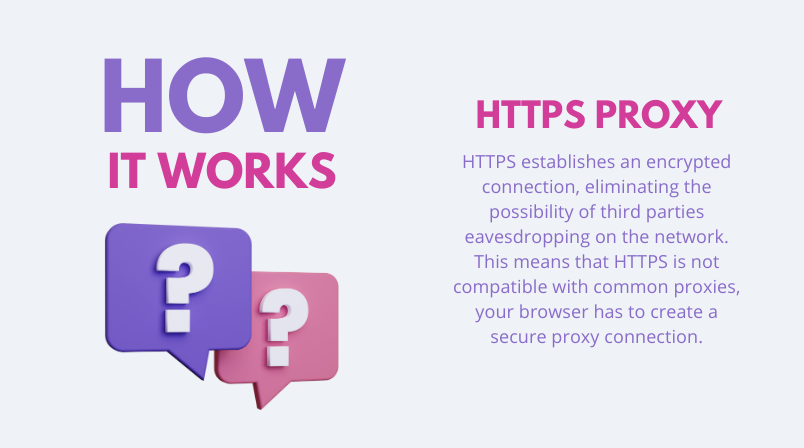
HTTPS establishes an encrypted connection, eliminating the possibility of third parties eavesdropping on the network. This means that HTTPS is not compatible with common proxies, your browser has to create a secure proxy connection. That’s why you need HTTPS supporting proxy OkeyProxy to promote your online works, with 150M+ real residential IPs, covering 200+ Countries, supporting all devices and use cases.
Initially, you need to connect to the server via a specific TCP port. These port numbers are somewhat arbitrary. However, server administrators can specify specific ports for specific purposes.
After this, the security process begins. Transport Layer Security (TLS) and the older Secure Sockets Layer (which we use at Green Prophet) are the two most common encryption methods used during joint work. These guidelines are intended to create a “chain of trust” in which each node in the communication chain is independently verified.
Differences Between HTTP Proxy And HTTPS Proxy
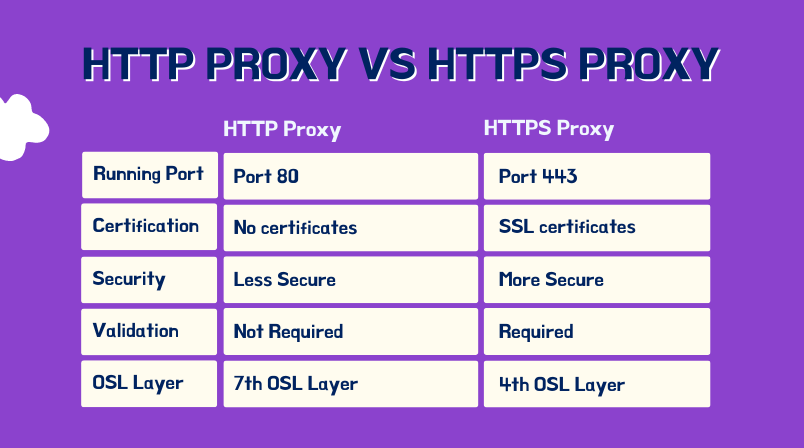
Using an HTTPS proxy can improve your online security and privacy in a variety of ways. While it is natural to draw comparisons between HTTP proxies and HTTPS proxies, there are significant differences between the two types.
The main difference between HTTP (https: //) and HTTP (http: //) is that HTTPS is a protocol that transmits data through Internet security. It uses the transport layer security (TLS) protocol Essence HTTPS is a combination of HTTP (protocol for transmitting data on the network) and TLS. In other words, HTTPS is an agreement based on a more basic TLS protocol.
HTTPS is more secure than HTTP because HTTPS applies digital certificates to encrypt and decrypt user page requests and the pages returned by the web server. Since HTTPS traffic is encrypted, it must be decrypted before it can be inspected. As security requirements increase, more websites, especially banking and online payment websites, are switching from HTTP to HTTP. Both HTTP and HTTPS proxy servers are available for download from the Internet. Surfing can be accelerated and network traffic can be reduced by using this feature.
Can You Use HTTP Proxy For HTTPS?
Technically, an HTTP proxy can be used for HTTPS traffic but does not provide any added security or encryption. The proxy will simply forward unencrypted HTTPS traffic between the client and server.
Aside from creating secure communication channels over insecure communication channels, communications engineers must also consider the benefits of HTTP vs. HTTPS proxies, as the latter uses SSL/TLS, which ensures end-to-end security.
What You Can Do With An HTTPS Proxy?
1. Maintain Anonymity: The IP address is one of the main identifiers of the online. It can be used to track, spy, and harass people. A proxy is a simple way to change the IP to prevent this problem, and the HTTPS proxy is the safest proxy type available.
2. Unblock Websites: Many websites block the content of users from other countries/regions. That is the reason for many people looking for proxies to listen to Spotify, watch YouTube videos, and access information from other countries/regions. Besides, proxies and s allow people to access various sites without any firewalls blocking them.
3. Web Data Scraping: There are many obstacles to collecting public information from the Internet. One of the most common problems is IP blocks and verification codes, which will prevent market researchers, data analysts, and other people who are trying to obtain the required data. They are often used in web scraping, where they can help avoid IP bans or blocks. By rotating your IP address, you can scrape data from websites without being detected or blocked. Thus, a proxy server from OkeyProxy is very useful. Analysts and researchers can use millions of unique HTTPS IP addresses as SSL proxies to obtain the data they need.
4. Testing and Debugging: Developers can use HTTPS proxies to test their applications’ behavior under different geographical locations or network conditions. This is especially useful when preparing an application for a global release.
5. Ad Verification: Advertisers can use HTTPS proxies to verify their ads’ proper display in different regions, ensuring that their campaigns are running as expected.
Conclusion
HTTPS proxies serve as a valuable tool in this endeavor, offering enhanced security, privacy protection, and the ability to bypass restrictions. By understanding how they work and what they apply for, you can ensure a safer and more secure browsing experience. To understand more, you can also read HTTP vs SOCKS Proxy: Comparing the Differences.